Sky Computing is a structural model for governing data, identity, policy, and control in distributed systems.
It addresses a fundamental shift in modern computing: systems no longer operate within a single environment. They span multiple clouds, sovereign domains, and edge deployments, where latency, partition, and regulatory constraints are normal—not exceptional.
Traditional architectures assume infrastructure defines authority.
Sky Computing inverts that assumption.
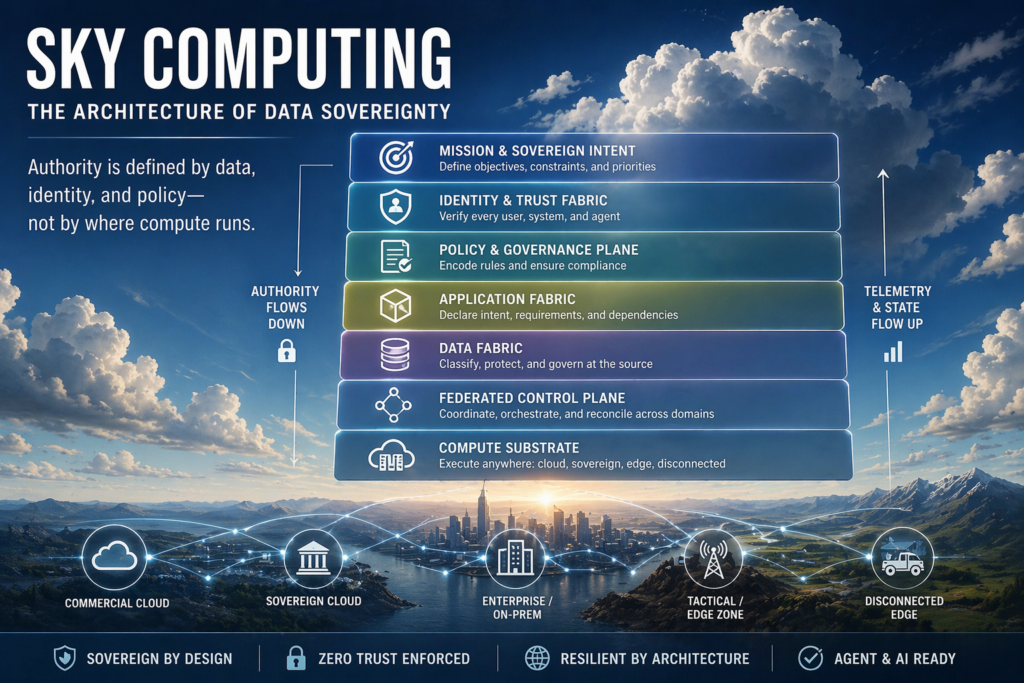
Authority is defined by data, identity, and policy—not by where compute runs.
The Core Idea
In cloud-era architectures, systems are built around infrastructure:
- data moves to where compute is available
- access is controlled by network boundaries
- governance is enforced per environment
This model works when systems are centralized.
It breaks when systems are distributed.
Sky Computing introduces a different structure:
- Data defines constraints (sovereignty, classification, handling rules)
- Identity defines access (who or what can act)
- Policy defines behavior (what is allowed, denied, or required)
- Control is federated across environments
- Compute becomes interchangeable
Infrastructure no longer defines authority.
It executes within it.
Why Sky Computing Exists
Modern systems operate under conditions that traditional architectures do not handle well:
- Partition is normal (cross-cloud latency, disconnected edge, contested networks)
- Sovereignty is enforced (data cannot move freely across jurisdictions)
- AI systems require local execution (data gravity prevents centralization)
- Multi-cloud environments create fragmentation (identity, policy, and control diverge)
The result is:
- inconsistent governance
- duplicated systems
- operational risk
- delayed or incorrect decisions
Sky Computing addresses these problems by making authority explicit and enforceable across environments.
The Sky Computing Model
Sky Computing is defined as a layered architecture:
- Mission & Sovereign Intent — defines priorities, constraints, and acceptable trade-offs
- Identity & Trust Fabric — establishes verifiable identities for users, systems, and agents
- Policy & Governance Plane — encodes rules as executable logic
- Application Fabric — declares workload intent and requirements
- Data Fabric — carries classification, lineage, and sovereignty constraints
- Federated Control Plane — coordinates behavior across domains without centralizing authority
- Compute Substrate — executes workloads across cloud, sovereign, and edge environments
Each layer is independent, but together they form a system where:
authority flows downward
telemetry and state flow upward
How Sky Computing Works
In a Sky-aligned system:
- Data is created with embedded classification and policy constraints
- Identity is verified locally without centralized dependency
- Policy is enforced at runtime before actions occur
- Control operates federated across domains
- Systems continue operating under partition and degraded conditions
- State is reconciled when connectivity returns
This allows organizations to:
- enforce sovereignty without blocking operations
- maintain availability where required
- preserve consistency where necessary
- operate coherently across environments
Sky Computing vs Existing Models
Sky Computing is not a replacement for existing approaches. It is the governing model that makes them coherent.
- Multi-cloud distributes infrastructure but does not define authority
- Zero Trust secures access but does not govern data or control
- Data Mesh assigns ownership but does not enforce sovereignty across domains
- Policy-as-Code encodes rules but does not define the structure they operate within
Sky Computing integrates these concepts into a single authority model.
A Simple Way to Understand It
If a system is distributed across multiple environments, ask:
- Who defines what data can do?
- Who defines who can act on it?
- Who enforces that decision?
If the answer changes depending on where the system runs:
the architecture is infrastructure-bound.
If the answer is consistent across environments:
the architecture is Sky-aligned.
Why It Matters
Organizations are already operating in distributed, sovereign, and partitioned environments.
The question is not whether these conditions exist.
It is whether systems are designed to handle them.
Sky Computing provides a framework to:
- align architecture with real-world constraints
- enforce governance without centralization
- enable AI and data-driven operations at scale
- maintain coherence across federated environments
Learn More
Sky Computing is defined in detail in:
Sky Computing: The Architecture of Data Sovereignty by Greg Bew
Reference architectures, implementation patterns, and evolving practices are maintained outside the book to reflect real-world deployment and change over time.